I received a set of Bit-Cards in the mail today, which I’d eagerly ordered last week. They look like credit cards, but work like somewhat like Casascius coins or another single-use paper wallet, with a hologram hiding the key, and they come in all sorts of denominations.
This is a very polished design, and they’re a pleasure simply to hold. You can scan the address directly with one QR code, and you can visit a link to their site with information about your particular card with the other.
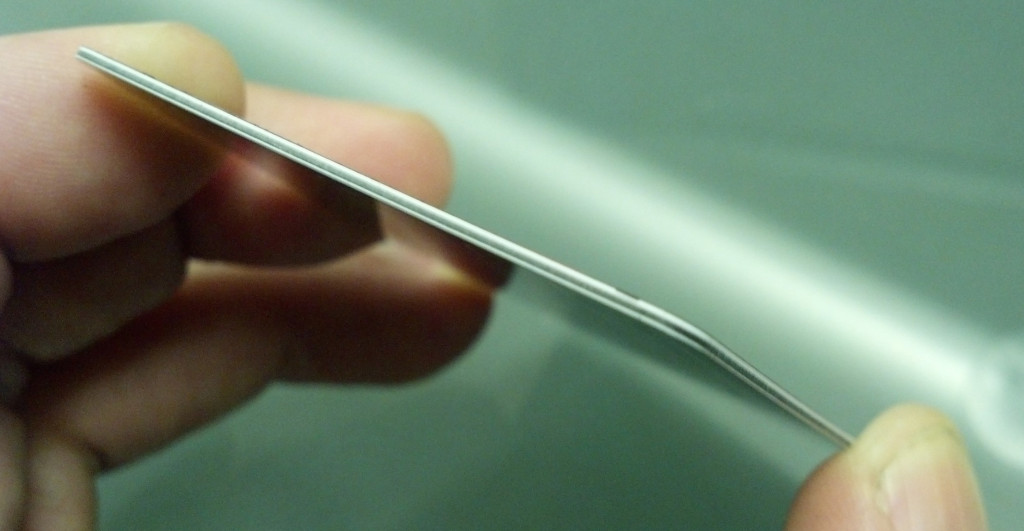
They profess to generate the keys and subsequently the cards on an off-line computer running custom software, and that they do not save the keys anywhere other than on the cards. Security features include the tamper-evident hologram as well as the multi-layer manufacturing of the card itself, so it is resistant to invasive scanning.
Scratch off the hologram, and the key is readily available to either scan, or type in manually.

The cards are shipped unfunded, and activated manually by the recipient through their online system upon receipt. The web site is as polished as the cards, from ordering through activation.
The non-denominated wallet-cards are intriguing, but you just have to keep coming back to the question: Why would I trust anyone else with my private key? In the case of a shiny collectible coin, it might seem worth some risk, but for a plastic card that’s a tougher sell, no matter how pretty the card.
Of what practical utility is a premade card with a set denomination of BTC on it, or an offline wallet the key to which has already been handled by someone else? That’s not entirely clear, but Bit-Card.de is at least establishing themselves in this space, and doing so with considerable style.

Standard disclaimer: It’s always, to some degree, a bad idea to let anyone else have access to a private key which controls any of your bitcoin wallets; in a sense, it goes counter to the bitcoin system itself. Once someone else has handled the key which controls your funds, you have to trust both that they exercised adequate security procedures while handling your key, and that they have not save copies of your key to exploit at some point in the unforeseen future. While some (such as Mike Caldwell of Casascius) have established trusted reputations, newer operators can only prove their trustworthiness over time.





